Please note that this post is not intended to provide health advise and should only be used for educational purposes. The following explanation is based on the work of Andrew Cutler, PhD, who is specialiced in the field of heavy metal toxicity. More information about hair testing can be found in Hair Test Interpretation: Finding Hidden Toxicities.
Introduction
Hair tests are historically used to determine the health status of a patient. It can be used to determine whether certain minerals are depleted or whether there is heavy metal toxicity. The problem with the former is that hair mineral levels might not represent body mineral levels. Either way, we are not really interested in that. What we want to know is how to determine when a hair test points in the direction of heavy metal poisoning.
The most common hair test is the ‘Toxic and Essential Elements’ test. This hair test measures the availability of toxins as well as the different essential elements in a hair sample.
There are a wide range of heavy metals that can be the cause of a certain health condition. The metal that can cause the most problems is mercury. Mercury interferes with the process that is responsible for the regulation of mineral concentration and how your body transports minerals. While other toxins can cause certain mineral transports, mercury causes a ‘general’ impairment. This is what can be called ‘deranged mineral transport’.
The hair test of people who are chronically mercury toxic usually show a mercury level that is within normal ranges. This is because these people have a hard time to get rid of mercury toxicity. Especially people who have detoxification problems will have a normal result for the toxic metals. This is why it can be hard to determine whether someone has mercury poisoning through a hair test.
Because it is hard to determine mercury toxicity based on the concentration of toxic metals in a hair sample, it has to be determined based on the concentrations of the essential elements. Because mercury interferes with the process of mineral transport, the concentrations of the essential elements will look ‘odd’.
Toxic metals
The first part of a hair test contains the toxic metals. Because we are talking about toxic metals, there is only an upper bound. If one of the toxins is in the red part of the chart, it may indicate toxicity. The scales that are being used are comparisons with what is seen in the general population. The lab will make a distinction between different sexes and ages. This means that the concentration of a certain element may be higher than the concentration of anther element, but is categorized in a lower percentile. A quotation in the 95th percentile means that this specific element has a concentration in the upper 5% which means that only 1 in 20 people have a similar or higher result. Please notice that this is not a linear scale. The 95th percentile is much wider than the 68th percentile. Next example is a hair test I have done myself in 2014.
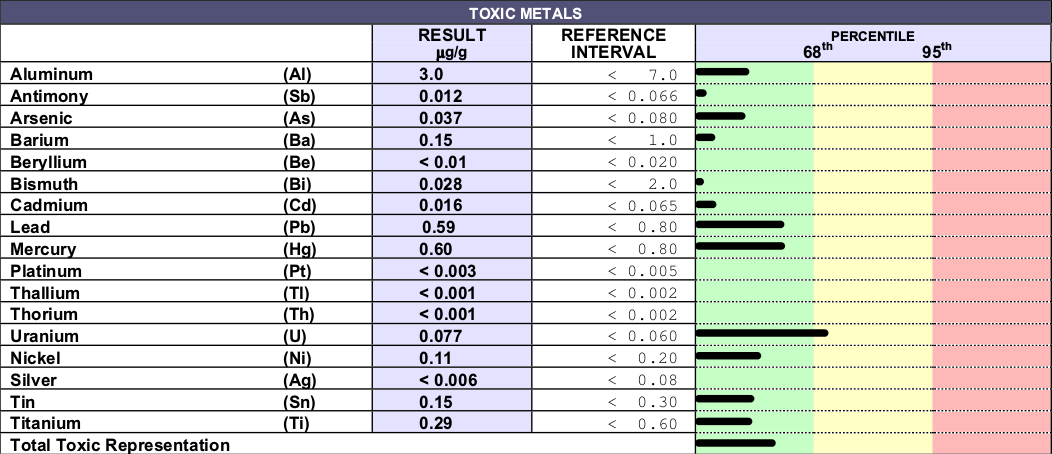
As you see, there is nothing special to see. Only Uranium is in the 68th percentile and mercury and lead are somewhat elevated.
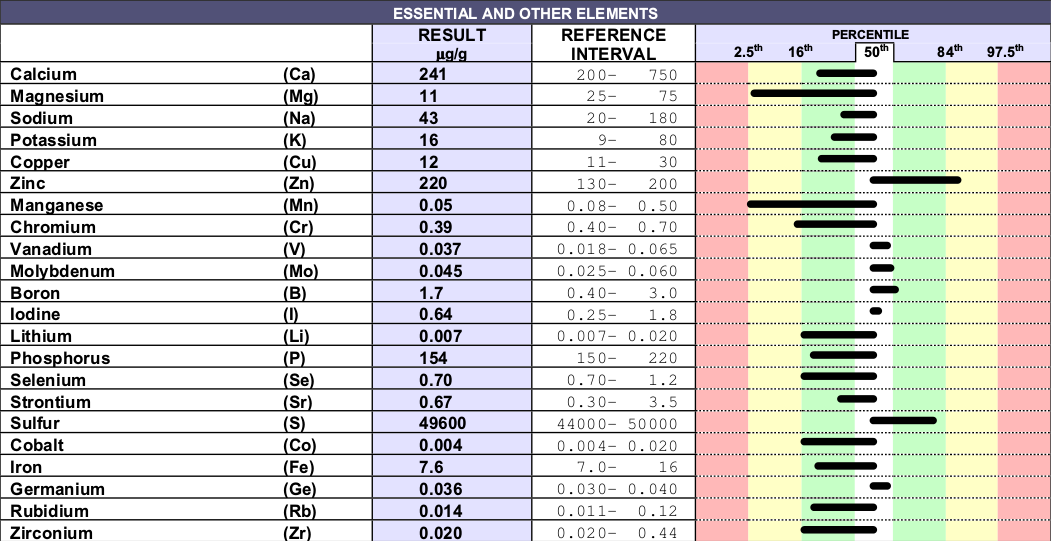
Essential and other elements
The second part of a hair test contains essential and other elements. The difference here is that there is also a lower bound. It’s important to notice that the concentration of the elements in hair samples don’t necessarily resemble the concentration of that element in the rest of the body, but it may be an indicator.
How can one recognize ‘deranged mineral transport’? As mentioned before, the result of each element is compared with the overall population. This means that we can calculate the probability that a certain phenomenon can happen. There are a few phenomena that can happen in a hair test.
- A lot of bars to the left or right.
- A lot of bars in the red.
- A small amount of bars in the green and white area.
Whether a certain count of bars in a certain area is significant is determined by basic statistics. Take for example the amount of bars to the left/right. The chance that a certain bar is located in either the left or right side is 50 percent. Assume that you have a hair test of 5 elements. There are 25 different kind of results. The chance that all bars point to the right is 1/25, since there is only one way to have 5 bars to the right. The chance that 4 bars point to the right is 5/25, since there are 5 ways to have 4 bars to the right. Saying that there are 4 bars to the right is the same as saying that there is 1 bar to the left, which obviously has the same chance of 5/25. All those chances should sum up to 1.
Obviously just calculating the chance that a certain amount of bars are to the left/right doesn’t say all that much. In the case of the hair test, there are 22 elements. 11 out of 22 elements to one side has a probability of 17% even though the hair test is perfectly normal. What we need to know is the probality that less than x amount of elements point to 1 side (or more, depending on how you want to calculate it). Which means that we have to count all the probabilities lower and equal to that amount. For 11 out of 22 this is exactly 0.58 which makes sense. This means that there is a 0.58 chance that there are less than 11 bars pointing to one side. If there would be 23 elements in total, the chance for 11 (or less) bars to 1 side is exactly 0.5. Think about why this is 🙂
Similar things can be done with the calculation for the bars in the red and in the green or white. The chance that a certain hair test appears with x bars in the red is 0.95(amount-x)*0.05x with ‘amount’ the total amount of elements. The chance that a certain hair test appears with x bars in the green or white area is 0.67x*0.33(amount-x) with ‘amount’ the total amount of elements.
When is a certain result significant? Cutler doesn’t really talk about percentages, rather about the amount of bars that are ‘off’.
- For the amount of bars to 1 side, 5 bars meet the counting rules (this means deranged mineral transport), 6 bars are suspicious, 7 are unusual, 8 not uncommon and 9 or higher is normal.
- For the amount of bars in the red, 4 bars or more meet the counting rules, 3 bars is unusual, 2 is uncommon and 1 or less is normal.
- For the amount of bars in the middle band, 11 or less meet the counting rules, 12 is suspicious, 13 is unusual, 14 is not uncommon and 15 or more is normal.
All these numbers are based on the fact that there are 23 elements in total, while the hair test we are trying to analyze has 22 elements. A quick lookup teaches us that the probabilities between 23 and 22 elements aren’t much different, which means that these numbers can be used for a hair test with 22 elements. For those interested in the exact numbers for 23 elements, 5 bars or less to one side equal a chance of 0.6%, 4 bars or more in the red equal a chance of 2.6%, 11 bars or less in the middle area equal a chance of 4.5%.
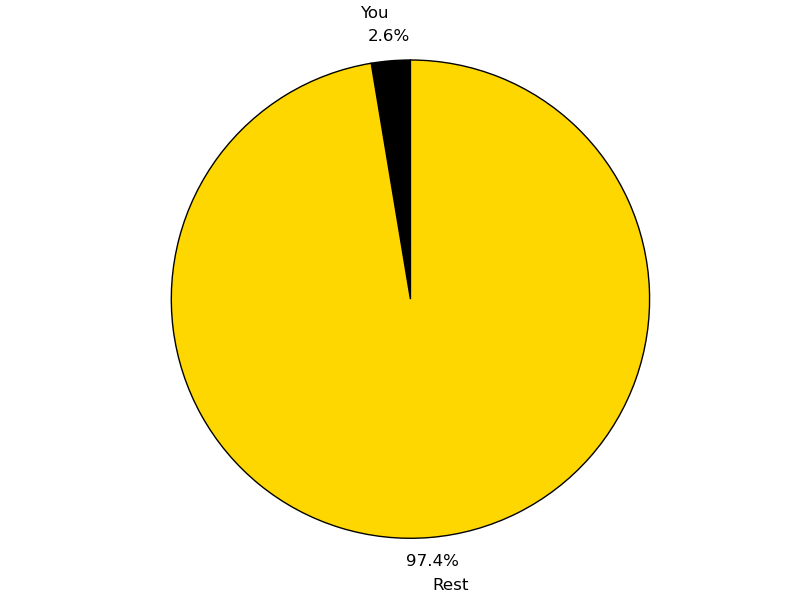
As we see in the example, one can quickly see that the amount of bars in the red (1) and the amount of bars in the middle (14/18, depending on whether you want to include the borderline cases) isn’t going to offer a statistical significant result. The amount of bars to 1 side is interesting. We see 7 bars to the right side which would be ‘unusual’. As you see, 5 of the 7 bars to the right are just slightly to the right, especially iodine. I have been supplementing with molybdenum and iodine in the recent past which may increase the levels of these elements. Because of this we only count 6 bars. This leads to a ‘suspicious’ hair test which has a probability of 2.6% (so it only occurs at random in 1 in 40 people). To represent it graphically:
The high levels of zinc may be caused by a zinc displacement by other metals like cadmium, lead, copper and mercury resulting in a paradoxially elevated hair zinc. Zinc hair levels may not be reliable because a lot of shampoos contain zinc.
The numbers that are published by Cutler are based on a hair test with 23 elements. More recent hair tests only include 22 essential elements (barium has been moved to the toxic metal area). Because of this, I’ve written a generic script (doesn’t work anymore) that will calculate the probabilities of your specific hair test.
The results of the hair test we discussed in this post are available here (doesn’t work anymore).
If there is a history of chronic conditions, mercury poisoning would be a very good explanation in this case.
If your test comes up positive, it’s really recommended to read Amalgam Illness, Diagnosis and Treatment by Cutler.
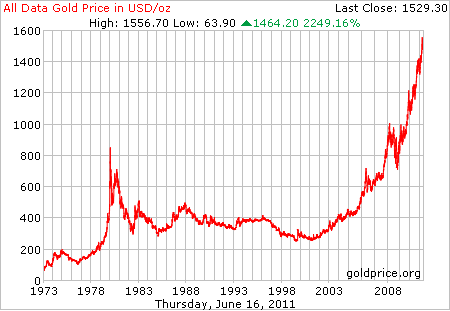
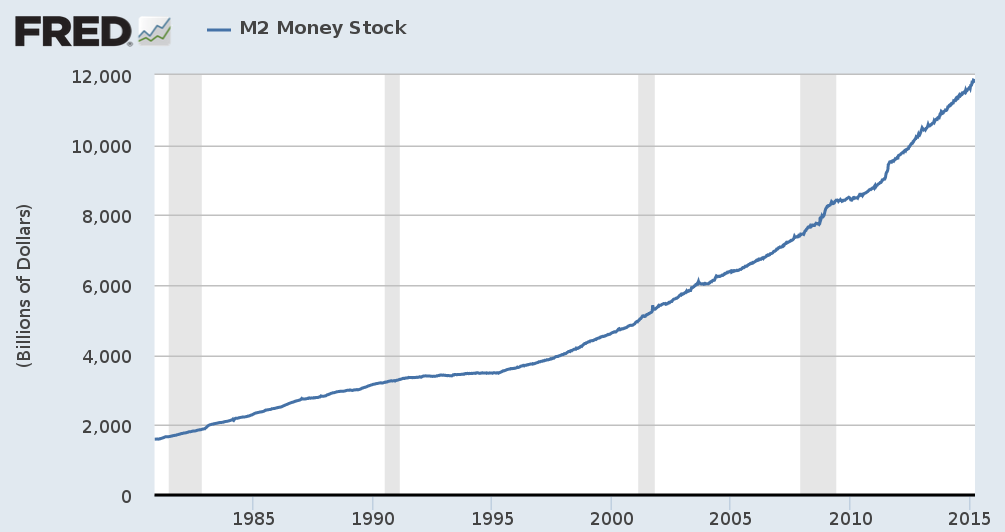 It’s not a wonder that the purchasing power of the dollar has dwindeled since the introduction of the Federal Reserve.
It’s not a wonder that the purchasing power of the dollar has dwindeled since the introduction of the Federal Reserve.
 To make the analogy with the internet, what if the internet would be centralized in one place. It would not be possible to expand the internet. The internet would just be a certain network somewhere in the world that has a fixed amount of routers, cables and data storage. Anyone in the world can connect to this network and it is the only network that will ever exist. In order to participate, you must buy a piece of this network from someone else. Everytime you use it, you have to sell a piece of your share to another participant on the network. There is no bottom on the price of a piece of this internet, nor is there a ceiling. Still, it would be an excellent store of value.
To make the analogy with the internet, what if the internet would be centralized in one place. It would not be possible to expand the internet. The internet would just be a certain network somewhere in the world that has a fixed amount of routers, cables and data storage. Anyone in the world can connect to this network and it is the only network that will ever exist. In order to participate, you must buy a piece of this network from someone else. Everytime you use it, you have to sell a piece of your share to another participant on the network. There is no bottom on the price of a piece of this internet, nor is there a ceiling. Still, it would be an excellent store of value.

 The person who has the private key in their possesion, can sign transactions. Everytime you want to do a transaction, you enter the receiver of the transaction (this can easily be done by scanning a QR code or even by wireless protocols), the amount of bitcoins you want to transfer and you sign this message with your private key. This message is broadcasted over the internet. Because your public key is added in the transaction, the signature can easily be verified. Of course this system alone would be an empty box. There is no cohesion in the system. How does someone receive bitcoins if there is no central authority involved? How can you make sure that the balance of someone changes when a transaction is made? In essense, bitcoin brings a solution to the
The person who has the private key in their possesion, can sign transactions. Everytime you want to do a transaction, you enter the receiver of the transaction (this can easily be done by scanning a QR code or even by wireless protocols), the amount of bitcoins you want to transfer and you sign this message with your private key. This message is broadcasted over the internet. Because your public key is added in the transaction, the signature can easily be verified. Of course this system alone would be an empty box. There is no cohesion in the system. How does someone receive bitcoins if there is no central authority involved? How can you make sure that the balance of someone changes when a transaction is made? In essense, bitcoin brings a solution to the